This guide provides the most up-to-date information on the Cyber Resilience Act (CRA), a European Union law that establishes mandatory cybersecurity requirements for products with digital elements.
If you manufacture, maintain, or steward open source software, you may be wondering how the CRA applies to you. CRA reporting requirements will become applicable on 11 September 2026, with all requirements taking effect on 11 December 2027 — so it’s important to begin preparing now.
Counting down to CRA compliance
Starting 11 September 2026, manufacturers must comply with vulnerability reporting requirements. Other CRA deadlines also apply.
About the Cyber Resilience Act
The Cyber Resilience Act (CRA) entered into force on 11 December 2024. CRA is a European law created to ensure that software products are designed and maintained with security in mind throughout their lifecycle.
Hardware and software products are increasingly subject to cyberattacks. The inherent security risks of software are not well understood by consumers, yet estimates predict that cybercrime will cost the global economy more than 20 trillion USD by 2026 (Source: Statista).
Manufacturers: a software vendor or a vendor of a physical product with software components. Manufacturers include anyone who is placing a product on the European market, i.e. this is not limited to European companies.
Open Source Maintainers: The EU is in the process of developing guidance on how the law will impact maintainers who monetize an open source project. If you just contribute to open source or do not monetize open source, you will not be impacted directly by the CRA. However, you may experience indirect impact in terms of higher expectations around security.
Open Source Stewards: Code hosting foundations or for-profit organizations that are not monetizing the particular pieces of software they are stewarding.
Not sure where your organisation fits? Check out the CRA FAQ.
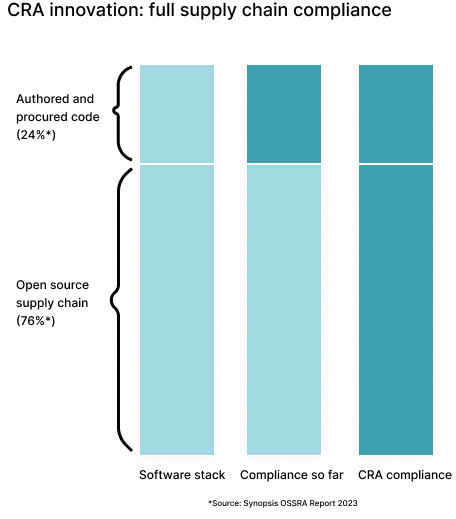
Full supply chain compliance has never been required before the CRA. In any kind of software application, about 24% is built in-house or procured and 76% is open source dependencies. The CRA impacts the entire supply chain, including the ~76% of OSS, in every product. This changes everything.
Compliance used to be internal policies and legal agreements with vendors. Now, the whole open source supply chain compliance will have to be brokered.
The fines are severe. Manufacturers will be fined if caught not in compliance. In addition to monetary fines, products will be removed from retail shelves until compliance is met.
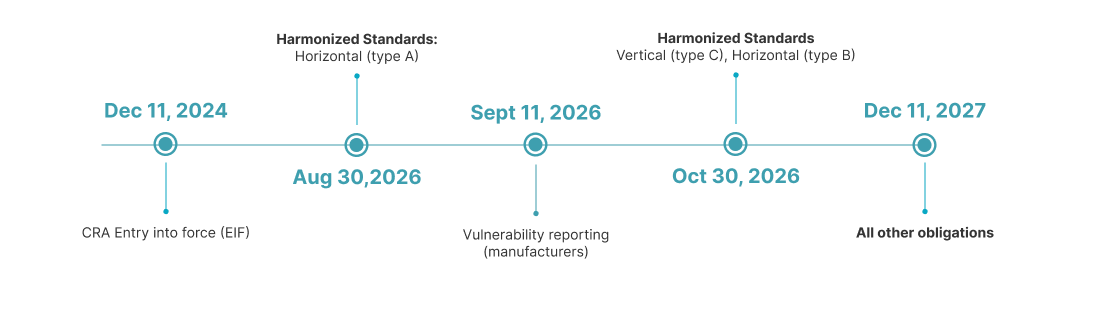
The Cyber Resilience Act (CRA) entered into force on 11 December 2024. Manufacturers must comply with vulnerability reporting requirements by 11 September 2026. Several compliance deadlines follow based on product classification: horizontal (type A) must comply by 30 August 2026, while vertical (type C) and horizontal (type B) have a compliance deadline of 30 October 2026. All other CRA obligations become fully applicable by 11 December 2027.
CRA Resources
Connect, Learn & Stay Up to Date on the CRA
Community Resources
In response to the evolving regulatory landscape introduced by the Cyber Resilience Act (CRA), the Open Regulatory Compliance (ORC) Working Group has mobilised a dedicated community effort to support open source stakeholders. Recognising the unique challenges faced by developers, maintainers, and organisations, we are collaboratively developing a comprehensive suite of resources designed to demystify the CRA and provide actionable guidance. Our key initiatives, each crafted through community input, empower stakeholders to achieve informed and effective compliance.
CRA Frequently Asked Questions (FAQ)
The ORC community is actively developing this FAQ to address common questions about the CRA’s impact on open source projects. It is a living resources that evolves as new insights emerge and as discussions with regulators progress.
Explore CRA FAQsEuropean Commission Resources for Implementation
The European Commission provides official guidance and frequently asked questions on the implementation of the CRA. These resources covers a wide range of topics, including the scope of the regulation, obligations for manufacturers and software providers, reporting requirements, and the evolving implementation timeline. It also includes guidance relevant to the open source ecosystem, helping clarify how the CRA applies across the broader digital supply chain.
Explore the EC's CRA ResourcesORC's Ongoing CRA Work and Community Contributions
The ORC community is continuously developing resources to help the open source ecosystem prepare for the CRA. This includes white papers, community inputs and contributions, and technical specifications that support understanding and practical implementation.
Learn More and Get InvolvedJoin the Discussion
Collaborate with us
The Open Regulatory Compliance (ORC) Working Group is a neutral forum for the open source community — including foundations, maintainers, vendors, users, package managers, among others — and the broader software industry to facilitate CRA compliance.
Status Legend
| Status | Meaning |
|---|---|
| 🗺️ Planned | Work has not yet started |
| ✍️ Work in Progress | Currently being developed |
| 🚀 Shipped | Complete and available |
| ❌ Cancelled | Will not be completed |
